Ever wanted to know what is going on over your home network?
Sure, you could install some IDS/IPS like Snort on a raspberry pi, configure some rules and go to town… OR you can write your own for fun! That’s what I did. Perhaps I took the road less travelled — ignoring the fact that some times the road less travelled is “less travelled” for a reason. But I digress.
I was curious about what was on my network and I had requirements. I wanted …
- A basic network scanner that will list all the IPs on my network (nmap)
- A detailed scan of each IP on my network (nmap)
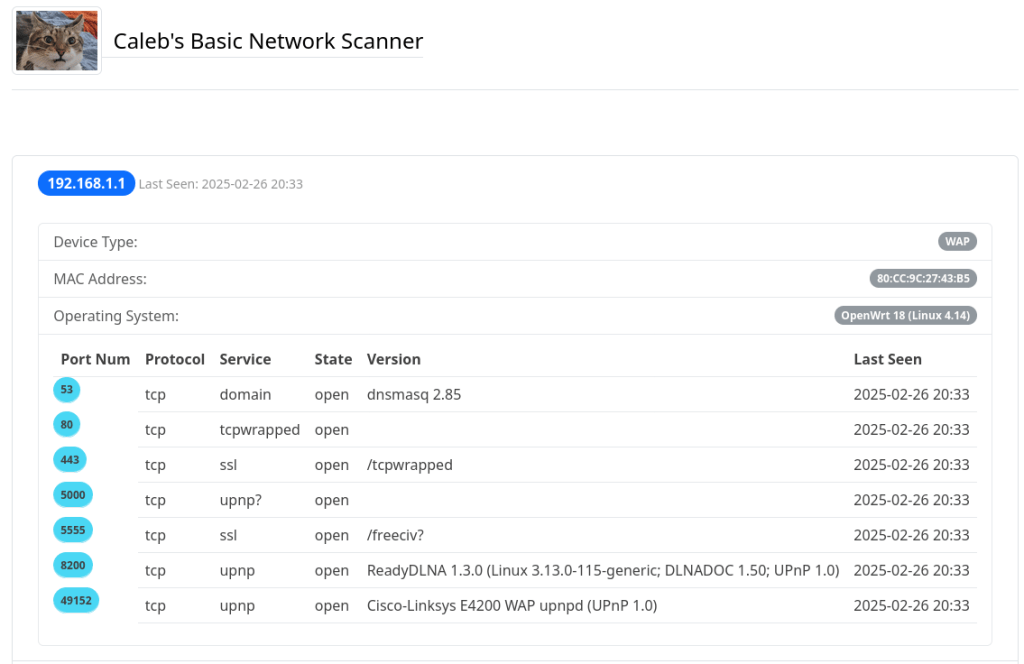
- A dashboard that showed the results and scans over time — including historic data showing ports seen in the past and ports now seen (try to find those pesky intermittent port-gremlins)
- Regular scans that updated the dashboard
I COULD have used something like OpenVAS or Nessus and played with the configs to do what I want, but I wasn’t looking for a vulnerability scanner or real complexity, more of a “Here’s a layout of the IPs and their port scans on your network” in a nice “live” display. The extra vulnerability look-ups weren’t really needed.
The final result (v1.0) is 270-ish lines of python and a single dashboard.html file — quite nice for me, as I plan to just kick it off on a basic raspberry pi with a dedicated monitor. Eventually, I plan to add alerting whenever a new IP or port pops up on my network.
Here’s the GitHub for those interested: Calebs Basic Network Scanner
And here’s a picture of the dashboard:

You must be logged in to post a comment.